Author: VLADIMIR TSAKANYAN
-
THE SHADOW ARCHITECTURE: DECODING THE SILENT SUBSTRATE OF GLOBAL POWER
The article discusses the evolution of power dynamics in the digital age, highlighting the emergence of “Shadow Architecture.” It examines incidents like Stuxnet and the Volt Typhoon campaign, demonstrating how cyber-kinetic threats target critical infrastructure. The call for better cybersecurity practices emphasizes the need to navigate a fractured digital landscape regulated by powerful tech entities.
-
How Modern Cyber Strategies Are Leaving Critical Infrastructure in the Shadows
Vladimir Tsakanyan The digital battlefield has fundamentally changed, yet many national cybersecurity strategies remain anchored to outdated assumptions about where threats originate and who bears responsibility for defense. Recent policy developments, particularly the United Kingdom’s refreshed government cyber action plan and similar initiatives across multiple nations, reveal a troubling pattern: governments are fortifying their own…
-

Darkness in Caracas: The Geopolitics of the First Major Cyber-Kinetic Coup
On January 4, 2026, U.S. Delta Force captured Nicolás Maduro and Cilia Flores in Venezuela through a cyber-kinetic operation named “Absolute Resolve.” This represents a shift in warfare tactics, combining cyberattacks with military action. The incident has broad geopolitical implications, signaling a new era of U.S. interventionist policy and challenging digital rights in Venezuela.
-

The Predator Files: How Spyware Sanctions Removal Reveals the Complexities of Cybersecurity Policy
The Trump administration’s lifting of sanctions on Intellexa executives marks a significant policy shift from the Biden era. This decision raises concerns about national security, human rights, and democratic governance, especially as the Predator spyware continues to threaten privacy and press freedom. The removal signifies a troubling accommodation of commercial surveillance in statecraft.
-

Churchill in the Digital War Room: A Grand Strategy Compared to the UK’s Cyber Power Vision
Vladimir Tsakanyan articulates how Winston Churchill would evaluate the UK’s cybersecurity strategy. He would commend its ambition but critique its peacetime compromises. Emphasizing national survival, he would demand stronger mandates for defense, intelligence-sharing, and a zero-tolerance policy on ransom payments, asserting that survival must precede responsibility in cybersecurity.
-

Napoleon in the Digital Trenches: A Commander’s Take on Modern Cybersecurity Policy
Vladimir Tsakanyan analyzes modern cybersecurity through the strategic lens of Napoleon Bonaparte. He advocates for centralized control, improved intelligence sharing, significant resource allocation, and clear doctrines of retaliation to enhance national cybersecurity. Napoleon’s approach emphasizes efficiency, unified command, and the projection of state power in the digital realm as essential for success.
-
Voltaire in the Server Room: An Enlightenment Critique of Modern Cybersecurity Policy
If Voltaire analyzed contemporary cybersecurity, he would view it as a battleground against tyranny rather than a technical issue. He would critique state surveillance, censorship, and technical obscurity, advocating for transparency, due process, and accountability. His recommendations for cybersecurity policy would focus on protecting individual rights while fostering reason and civil liberties in the digital…
-

Cyber-Resilience and Economic Statecraft: The G7’s Diplomatic Push for Collective Financial Defense
The G7’s “Fundamental Elements” for Cyber-Incident Response emphasizes global cooperation to bolster the financial sector against cyber threats. It highlights economic stability as a national security interest and promotes a multistakeholder approach. This framework aims to establish clear norms for incident response, enhancing resilience and fostering trust among nations during crises.
-

Cybersecurity Policy Pivot: Analyzing the White House’s New Executive Order and Its Impact on Government Contractors
The June 2025 Executive Order shifts federal cybersecurity policy towards flexibility and targeted enforcement. It reduces compliance burdens while maintaining essential security mandates. Key changes include eliminating centralized software attestations, narrowing cyber sanctions, and emphasizing NIST standards. Contractors must adapt by focusing on strengthening core systems and ensuring compliance with evolving NIST guidance.
-
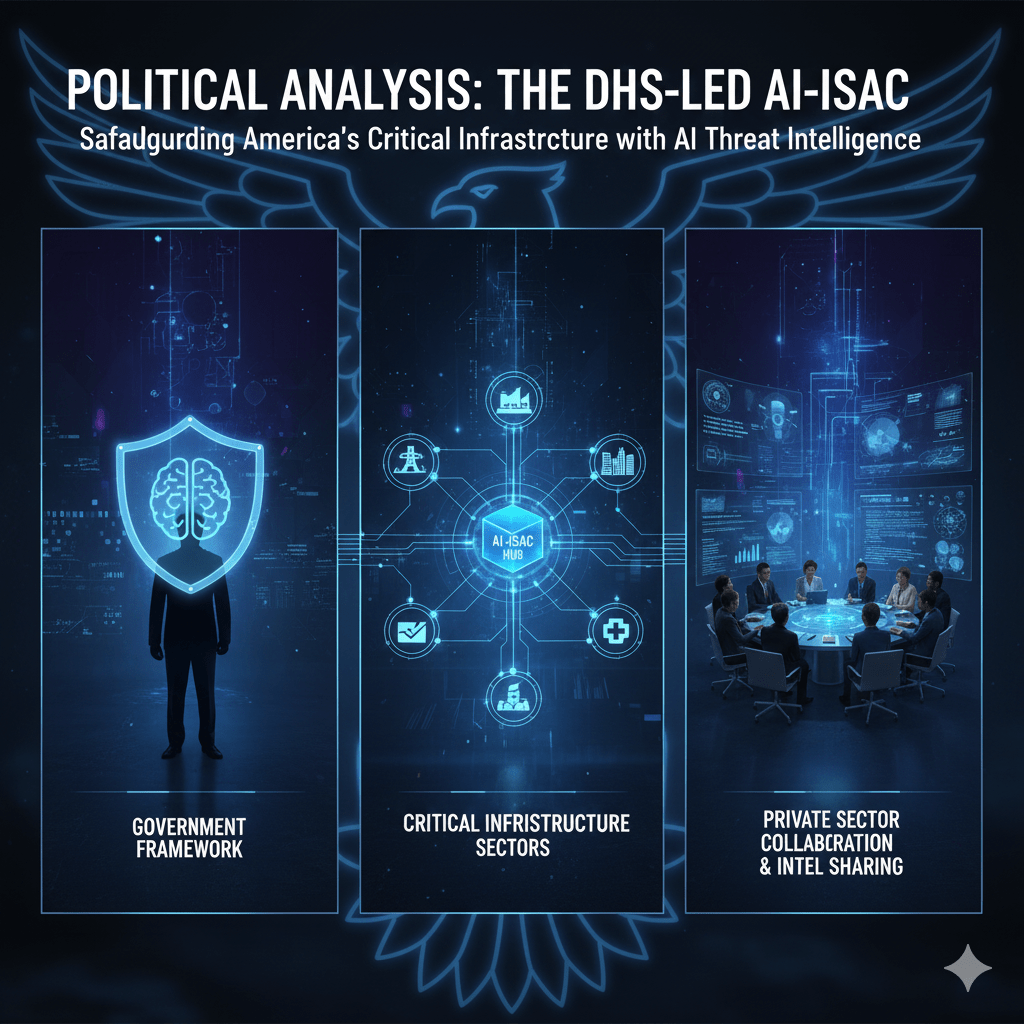
The DHS-Led AI-ISAC and the Future of Critical Infrastructure Security
The establishment of the Artificial Intelligence Information Sharing and Analysis Center (AI-ISAC) by the Department of Homeland Security is a strategic move aimed at enhancing national security by sharing AI-related threat intelligence. While the initiative is politically supported, challenges include fostering private sector collaboration and coordinating with existing agencies to avoid bureaucratic conflicts.
