Tag: ai
-
The New Ambassadors: Why Tech Companies Have Become Sovereign Actors in Global Diplomacy
In 2017, Denmark pioneered tech diplomacy by appointing a tech ambassador in Silicon Valley, recognizing the geopolitical influence of tech firms. Today, over seventy nations have embraced this model. However, despite diplomatic engagement, a significant accountability vacuum remains, complicating the regulation of powerful non-state tech actors in global governance.
-
Harvest Now, Decrypt Later: The Quiet Crisis in Post-Quantum Cryptography
Adversaries are storing encrypted communications, awaiting advances in quantum computing to read them, raising urgent concerns for organizations. As the timeline for quantum threats narrows, migration to post-quantum cryptography (PQC) is critical. Organizations must prioritize their cryptographic inventory and adopt quantum-resistant algorithms to safeguard sensitive data before it’s compromised.
-
The Price of Neglect: Critical Infrastructure and the Political Economy of Chronic Underinvestment
The vulnerabilities in U.S. critical infrastructure stem from political decisions, not just technical failures. Factors such as budget cycles, regulatory frameworks, and deferred accountability lead to outdated systems. A lack of serious investment in cybersecurity, combined with insufficient liability reforms, exposes infrastructure to threats that could be catastrophic if activated.
-
The Compliance Illusion: Why Cybersecurity Regulation Is Producing the Wrong Kind of Security
Governments are rapidly implementing cybersecurity regulations, but the fragmented nature and differing timelines often hinder effectiveness. Compliance can overshadow actual security, creating a two-tier environment where larger organizations exploit gaps while smaller entities struggle. Improved regulation should focus on outcomes rather than mere documentation to enhance security and accountability.
-
No Rules in the Room: The Diplomatic Vacuum at the Heart of Autonomous Cyber War
In March 2020, a Turkish-manufactured autonomous drone reportedly hunted down and engaged a human target in Libya without receiving a command from any human operator. The UN Panel of Experts documented the incident. No government acknowledged it. No legal mechanism was triggered. No one was held responsible. That episode is not a warning of what…
-
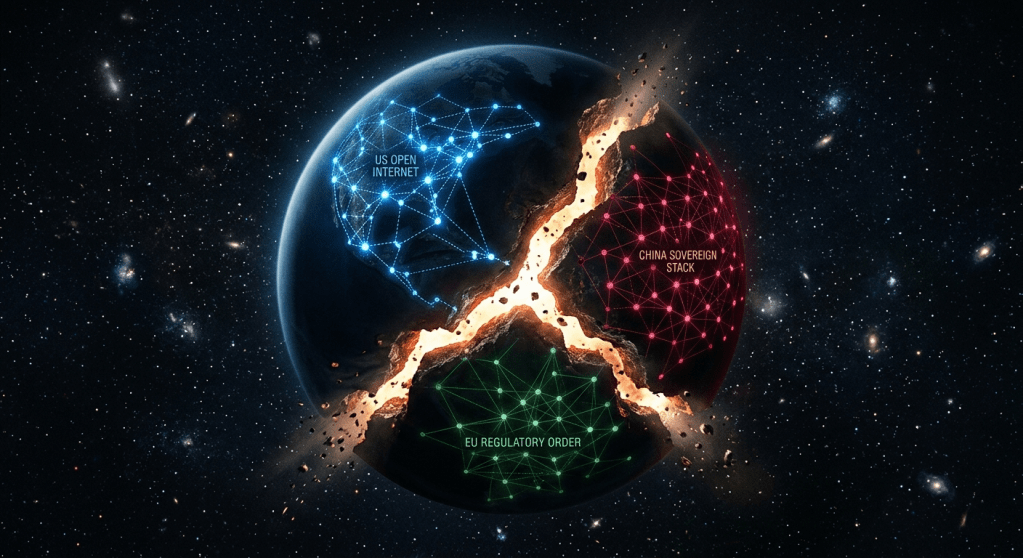
The Splinternet Doctrine: How Nation-States Are Redrawing the Map of Cyberspace
The internet’s borderless nature is being systematically dismantled, with countries pursuing digital sovereignty through distinct governance models. The U.S. advocates a free internet, while China promotes a sovereign model. This fragmentation poses challenges for diplomacy, commerce, and security, reshaping the landscape of global internet governance into a complex, multi-jurisdictional environment.
-
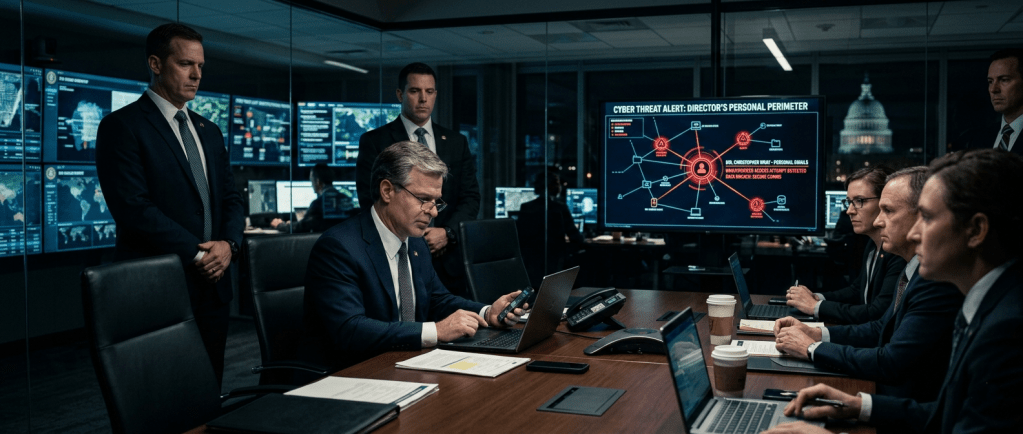
The Personal Perimeter: How Officials Become Targets
The report highlights how adversaries increasingly target the personal digital lives of government officials, emphasizing the evolving threat to national security from cyber warfare and information manipulation.
-
Why More Power Means Less Stability: 5 Surprising Truths About the New Cyber World Order
Cybersecurity faces complexity; traditional defenses may destabilize as middle powers emerge as stabilizers.
-
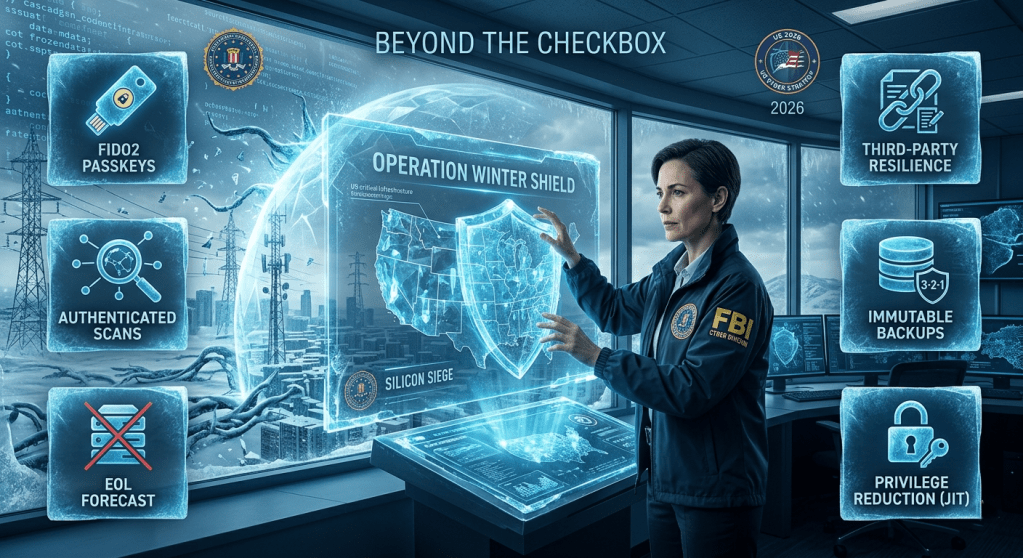
Beyond the Checkbox: 6 Hard-Hitting Truths from the FBI’s “Operation Winter SHIELD”
The FBI’s Operation Winter SHIELD addresses persistent cyber threats to American infrastructure, emphasizing a shift from reactive measures to proactive strategies for resilience. It outlines six mandates for organizations, including eliminating vulnerable authentication methods, managing third-party risks, securing backups, and reducing administrative privileges to deter adversaries effectively.
-

The “Elite” Hack That Wasn’t: 4 Surprising Truths Behind the Stryker Cyberattack
It turns out the “sophisticated” Stryker hack was less Mr. Robot and more “forgotten password.” 🔑💨 Behind the headlines of digital vengeance lies a story of hijacked admin tools and a very confused Wikipedia search. Read the 4 truths that strip away the “elite” hacker myth. #CyberSecurity #Stryker #TechUpdate #Hackers #DigitalWarfare
