Tag: news
-
The Compliance Illusion: Why Cybersecurity Regulation Is Producing the Wrong Kind of Security
Governments are rapidly implementing cybersecurity regulations, but the fragmented nature and differing timelines often hinder effectiveness. Compliance can overshadow actual security, creating a two-tier environment where larger organizations exploit gaps while smaller entities struggle. Improved regulation should focus on outcomes rather than mere documentation to enhance security and accountability.
-
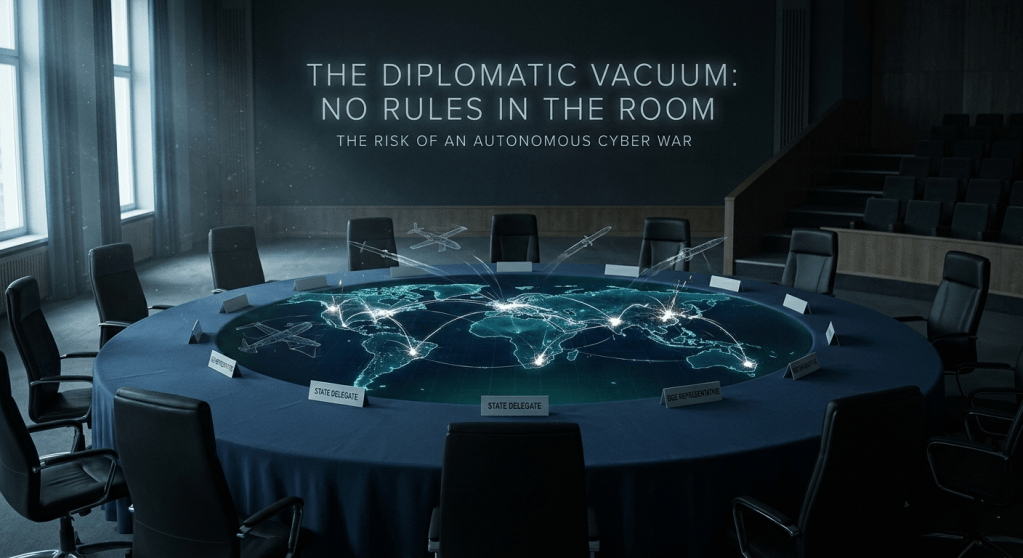
No Rules in the Room: The Diplomatic Vacuum at the Heart of Autonomous Cyber War
In March 2020, a Turkish-manufactured autonomous drone reportedly hunted down and engaged a human target in Libya without receiving a command from any human operator. The UN Panel of Experts documented the incident. No government acknowledged it. No legal mechanism was triggered. No one was held responsible. That episode is not a warning of what…
-
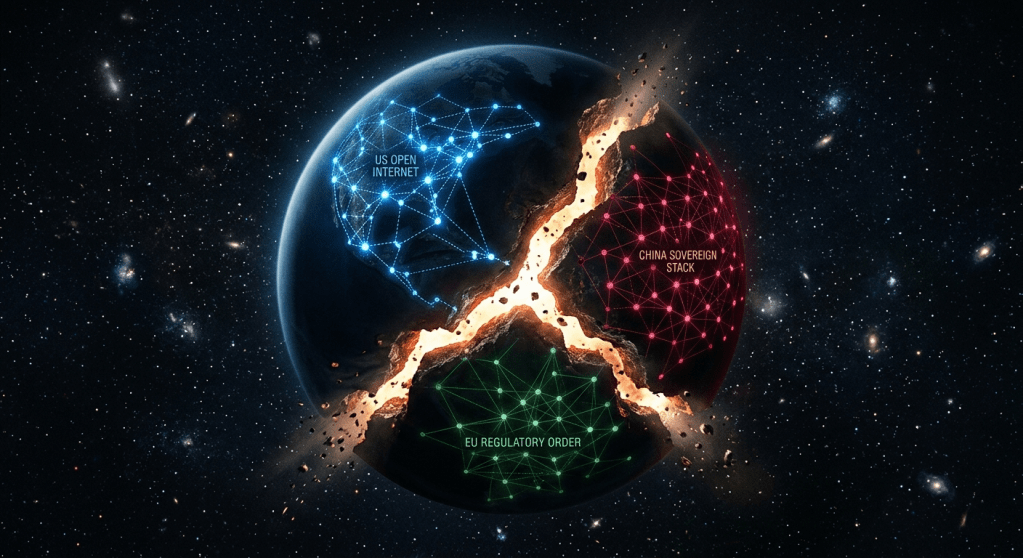
The Splinternet Doctrine: How Nation-States Are Redrawing the Map of Cyberspace
The internet’s borderless nature is being systematically dismantled, with countries pursuing digital sovereignty through distinct governance models. The U.S. advocates a free internet, while China promotes a sovereign model. This fragmentation poses challenges for diplomacy, commerce, and security, reshaping the landscape of global internet governance into a complex, multi-jurisdictional environment.
-
The Personal Perimeter: How Officials Become Targets
The report highlights how adversaries increasingly target the personal digital lives of government officials, emphasizing the evolving threat to national security from cyber warfare and information manipulation.
-
Why More Power Means Less Stability: 5 Surprising Truths About the New Cyber World Order
Cybersecurity faces complexity; traditional defenses may destabilize as middle powers emerge as stabilizers.
-
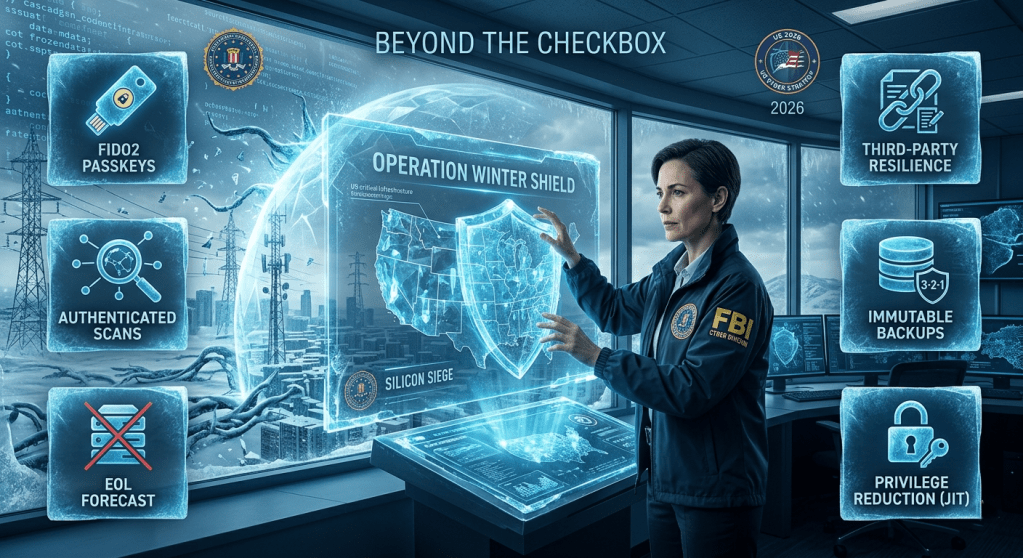
Beyond the Checkbox: 6 Hard-Hitting Truths from the FBI’s “Operation Winter SHIELD”
The FBI’s Operation Winter SHIELD addresses persistent cyber threats to American infrastructure, emphasizing a shift from reactive measures to proactive strategies for resilience. It outlines six mandates for organizations, including eliminating vulnerable authentication methods, managing third-party risks, securing backups, and reducing administrative privileges to deter adversaries effectively.
-

The Digital Iron Curtain: 5 Surprising Realities of Moscow’s Great Internet Blackout
Moscow is experiencing a technological regression, reminiscent of the 1990s, as state-imposed restrictions decay its digital infrastructure. With skyrocketing demand for analog devices and decreasing economic vitality, the government is testing a “Splinternet,” driven by fears of internal dissent. This situation poses questions about the city’s future amid increasing censorship and surveillance.
-

THE DIGITAL FRONTLINES OF THE IRAN WAR:
How Geopolitics Weaponized Cyberspace — and Left America Exposed By the CyberCenter Editorial Team | Political & Security AnalysisVladimir Tsakanyan When the United States and Israel launched a sweeping air and sea bombingcampaign against Iranian military and government assets on February 28,2026, the kinetic strikes were only one dimension of the conflict thatfollowed. Within hours,…
-
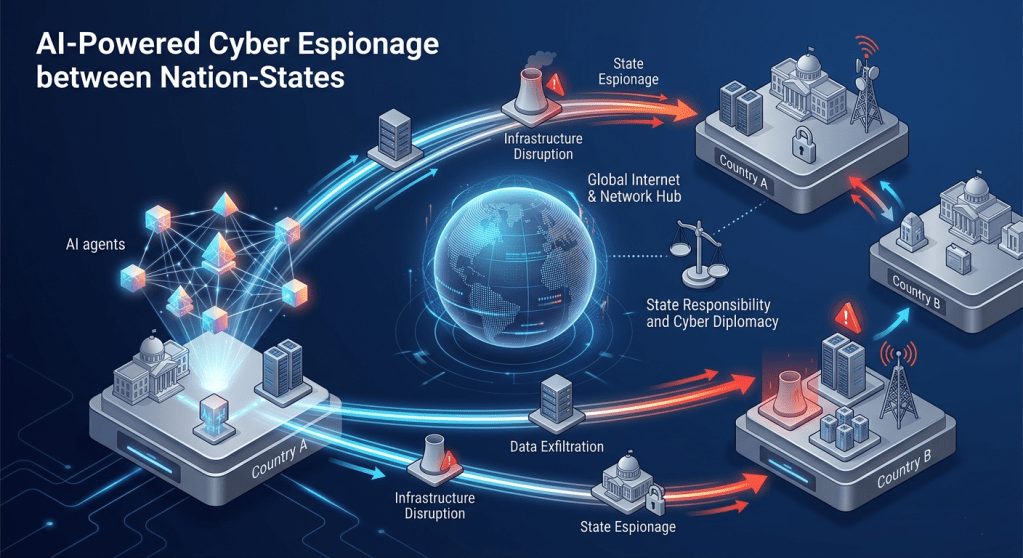
AI‑Supercharged Espionage: What Autonomous Cyber Operations Mean for State Responsibility and Cyber Diplomacy
Artificial intelligence is transforming cyber espionage, making operations faster and more autonomous. This raises legal and diplomatic challenges regarding state responsibility, as AI can complicate attribution and accountability. As AI-driven campaigns deepen and accelerating, the need for rigorous oversight and evolving cyber diplomacy is critical to address new risks and maintain international norms.
-
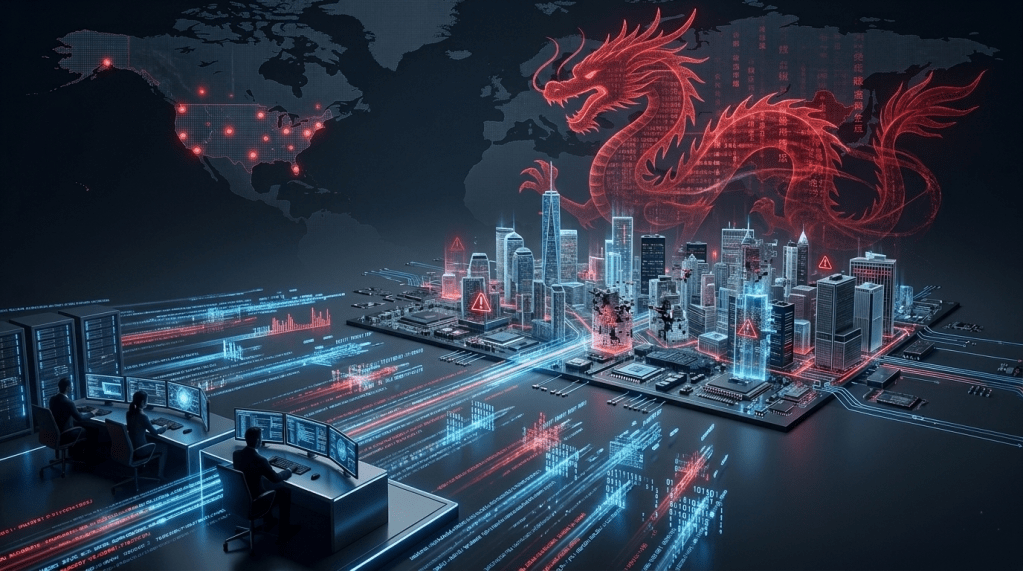
Washington’s New Cyber Strategy on China: Tough Talk, Weak Armor
The Trump administration’s new cyber strategy casts China as the U.S.’s main cyber threat, emphasizing an offensive approach. However, this strategy misidentifies the challenge by prioritizing aggression over crucial defensive measures. The approach risks leaving U.S. infrastructure exposed while failing to effectively connect cyber operations with broader policy tools against China.
