The digital battlefield has fundamentally changed, yet many national cybersecurity strategies remain anchored to outdated assumptions about where threats originate and who bears responsibility for defense. Recent policy developments, particularly the United Kingdom’s refreshed government cyber action plan and similar initiatives across multiple nations, reveal a troubling pattern: governments are fortifying their own digital walls while the critical infrastructure and private enterprises that underpin modern society remain comparatively exposed to increasingly sophisticated threats.
This isn’t merely an academic concern or a matter of bureaucratic oversight. The gap between government-focused cyber resilience and the protection of private sector critical infrastructure represents one of the most significant vulnerabilities in modern national security architecture. As artificial intelligence transforms the threat landscape and state-sponsored actors become more brazen in their campaigns, this strategic blind spot threatens to undermine the very foundations of economic stability and public safety.
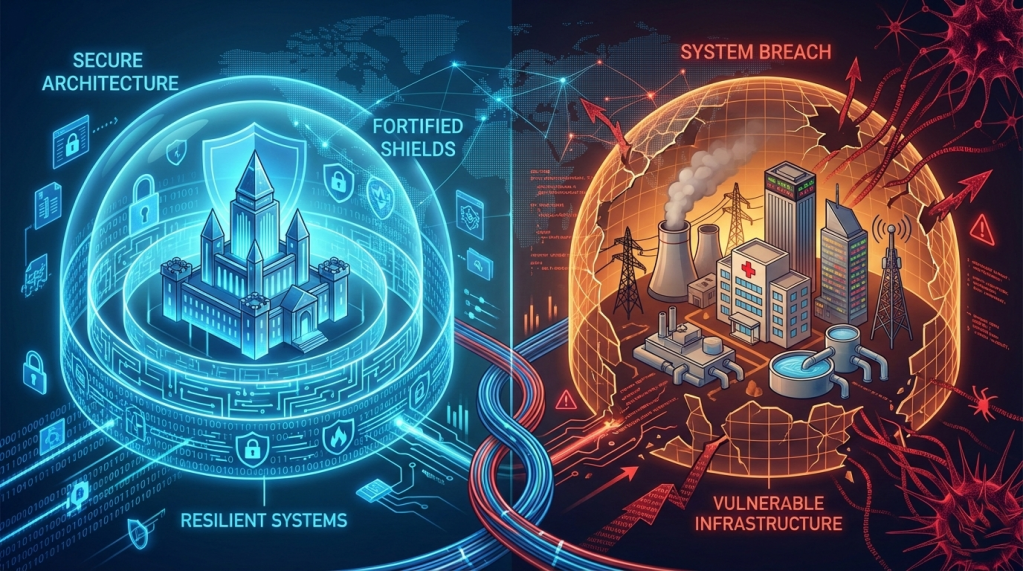
The Castle and the Town: Understanding the Strategy Gap
Imagine a medieval kingdom where the monarch invests enormous resources in making the royal castle impregnable—thick walls, deep moats, elite guards—while the surrounding town, which produces the food, manufactures the weapons, and houses the population, receives only vague suggestions about securing their homes. When invaders arrive, they bypass the fortress entirely and set fire to the undefended grain stores, blacksmith shops, and homes. The castle stands strong, but the kingdom collapses.
This analogy captures the essence of current cybersecurity policy approaches in the UK and numerous other nations. Government networks are receiving concentrated attention, robust frameworks, and dedicated resources. Meanwhile, the energy grids, telecommunications networks, financial systems, water treatment facilities, and healthcare infrastructure that constitute critical national infrastructure operate under a patchwork of regulations, voluntary frameworks, and market-driven security decisions.
The UK’s recent cyber action plan exemplifies this approach. While it outlines comprehensive measures for strengthening government digital defenses, incident response capabilities, and public sector resilience, it provides remarkably little concrete guidance for the private companies operating the infrastructure upon which national security and economic prosperity depend. This isn’t unique to Britain. Similar patterns emerge in national strategies from Australia to Canada, from Germany to Japan.
The fundamental challenge is that modern critical infrastructure is overwhelmingly owned and operated by private entities. In most developed nations, private companies control between seventy and ninety percent of critical infrastructure assets. Energy production and distribution, telecommunications networks, financial services, healthcare systems, transportation networks—all primarily exist in private hands. Yet national cybersecurity strategies continue to be structured as if the government sector represents the primary target and the primary responsibility.
The Evolution of Threat Actors: From Opportunists to Strategic Adversaries
To understand why this policy gap matters so urgently now, we must examine how cyber threats have evolved. The threat landscape of 2025 bears little resemblance to that of even a decade ago, yet many policy frameworks remain rooted in earlier paradigms.
Early cybersecurity threats were predominantly opportunistic. Individual hackers sought notoriety or financial gain through relatively unsophisticated attacks against targets of convenience. Defenses focused on perimeter security—firewalls, antivirus software, basic access controls. This model worked reasonably well when threats were sporadic and attackers lacked significant resources or coordination.
The landscape shifted dramatically with the emergence of organized cybercrime and, more significantly, state-sponsored cyber operations. Nation-states bring capabilities that dwarf those of individual actors or even sophisticated criminal organizations. They possess vast financial resources, technical expertise, legal immunity from prosecution, and most importantly, strategic patience. Where a criminal group seeks immediate financial return, a state-sponsored operation might spend years establishing access, understanding systems, and positioning capabilities for future exploitation.
These state-linked campaigns have consistently demonstrated a preference for targeting critical infrastructure and private sector entities rather than government networks directly. The reasons are both practical and strategic. Government networks, while valuable targets, typically receive more security attention, face more stringent compliance requirements, and are operated by personnel with security clearances and specialized training. Critical infrastructure, conversely, often operates on legacy systems, faces budget constraints that limit security investments, and employs personnel whose primary expertise is in engineering or business operations rather than cybersecurity.
Moreover, disrupting critical infrastructure offers adversaries asymmetric advantages. Compromising a power grid, telecommunications network, or financial system can create cascading effects that undermine public confidence, disrupt economic activity, and strain government resources far more effectively than breaching a government email system. The 2015 and 2016 attacks on Ukraine’s power grid demonstrated this principle vividly, as did the Colonial Pipeline ransomware incident in 2021, which caused widespread fuel shortages along the American East Coast despite affecting only a single private company’s billing system.
Artificial Intelligence: The Threat Multiplier Nobody Fully Understands
The integration of artificial intelligence into both offensive and defensive cyber capabilities represents perhaps the most significant transformation in the threat landscape since the internet itself became a domain of strategic competition. Yet the policy response to AI-driven threats reveals the limitations of current strategic thinking.
Artificial intelligence fundamentally changes the economics and scale of cyber operations. Tasks that previously required human expertise and time—identifying vulnerabilities, crafting social engineering messages, analyzing network traffic patterns, adapting exploits to specific environments—can increasingly be automated or augmented by AI systems. This doesn’t mean AI will replace human attackers, but rather that it enables both more sophisticated operations and dramatically increased scale.
Consider the traditional reconnaissance phase of a cyber operation. An attacker seeking to compromise a specific organization would manually research the company, identify personnel, analyze publicly available information, and craft targeted phishing messages. This process required significant time and expertise. AI systems can now automate much of this process, analyzing vast datasets to identify potential targets, generating convincing phishing content in multiple languages, and continuously adapting approaches based on what succeeds or fails.
The defensive implications are equally significant. AI enables defenders to analyze network traffic patterns, identify anomalies, and respond to incidents faster than human operators alone. But this creates an arms race dynamic where both attackers and defenders leverage AI capabilities, with advantage shifting to whoever can deploy more sophisticated systems or exploit gaps in the adversary’s approach.
National cybersecurity strategies are beginning to acknowledge AI-driven threats, but the policy responses often lack specificity or actionable guidance, particularly for private sector entities. Acknowledging that AI poses new risks is different from providing frameworks, resources, or requirements that enable organizations to understand and address those risks effectively.
The challenge is compounded by the reality that AI capabilities are diffusing rapidly. State-sponsored actors no longer monopolize access to sophisticated AI tools. Criminal organizations, activist groups, and even individuals can access powerful AI systems through commercial services or open-source projects. This democratization of capability means that the threat landscape includes both highly sophisticated state operations and an expanding array of other actors with capabilities that would have been beyond reach just years ago.
Supply Chain Vulnerabilities: The Invisible Attack Surface
While governments focus on hardening their own networks, one of the most significant threat vectors remains largely unaddressed in most national strategies: supply chain compromise. This attack method exploits a fundamental reality of modern technology—nearly every digital system incorporates components, software, or services provided by external vendors, creating a complex web of dependencies that attackers can exploit.
Supply chain attacks are particularly insidious because they undermine the very concept of a security perimeter. An organization can implement exemplary security practices for its own systems yet remain vulnerable if a software vendor, hardware manufacturer, or service provider in its supply chain is compromised. The attacker doesn’t need to breach the target’s defenses directly; they simply contaminate a trusted source that the target organization relies upon.
The SolarWinds compromise, discovered in late 2020, demonstrated the devastating potential of this approach. By compromising the software build process at a widely used IT management platform, attackers—believed to be Russian state-sponsored actors—gained access to thousands of organizations, including numerous government agencies and major corporations. The victims implemented the compromised updates themselves, believing they were applying legitimate security patches and software improvements.
This incident should have triggered fundamental policy reassessment regarding supply chain security, yet most national cybersecurity strategies continue to treat supply chain risks as a secondary concern or address them through vague commitments to “enhance supply chain security” without substantive requirements or resources.
The challenge extends beyond software supply chains. Hardware components, particularly those manufactured in regions with sophisticated cyber capabilities, present similar risks. Telecommunications equipment, networking gear, computer processors, and even peripheral devices can potentially incorporate malicious components or backdoors that enable remote access or data exfiltration.
Private companies operating critical infrastructure face particular challenges with supply chain security. They must balance security considerations against cost constraints, compatibility requirements, and operational needs. A power company cannot simply stop using all equipment from vendors that might pose supply chain risks—the operational consequences would be catastrophic. Yet without clear policy guidance, regulatory requirements, or government support, individual companies must make these risk decisions in isolation, often without access to the threat intelligence needed to assess risks accurately.
The Asymmetry of Information and Resources
One of the most significant yet underappreciated challenges in cybersecurity policy is the fundamental asymmetry between government capabilities and private sector resources, particularly for smaller organizations operating critical infrastructure.
Government intelligence agencies have access to threat intelligence, technical capabilities, and resources that far exceed what most private entities can marshal. They monitor global cyber operations, track threat actor groups, observe attack patterns, and develop sophisticated defensive and offensive capabilities. This information could be enormously valuable to private sector organizations defending critical infrastructure, yet information sharing remains inconsistent, often delayed, and frequently lacking in actionable detail.
Consider a regional electric utility or water treatment facility. These organizations operate genuinely critical infrastructure—their compromise could affect thousands or millions of people—yet they typically lack dedicated cybersecurity teams, threat intelligence feeds, or the technical expertise to understand and respond to sophisticated threats. When a government strategy emphasizes resilience without providing these organizations with the intelligence, tools, or resources needed to achieve it, the strategy amounts to aspirational rhetoric rather than actionable policy.
The asymmetry extends to incident response capabilities. When a government network is compromised, the response typically involves specialized teams with extensive resources and authority. When a private company suffers a breach, it must navigate a complex landscape of legal obligations, regulatory requirements, potential liability, and market pressures, often while lacking the internal expertise to manage the technical response effectively.
Some national strategies have begun to address this asymmetry through information sharing initiatives, public-private partnerships, and support programs, but these efforts remain limited in scope and impact. The UK’s National Cyber Security Centre, for instance, provides valuable guidance and services, but its primary focus and resources remain oriented toward government and the largest enterprises rather than the mid-sized companies that collectively operate much of the nation’s critical infrastructure.
The Regulatory Patchwork: Compliance Without Security
In the absence of comprehensive national strategies that effectively address critical infrastructure protection, many countries have developed sector-specific regulations and compliance frameworks. Energy sector operators face certain requirements, financial institutions face others, healthcare providers face still others. This patchwork approach creates several significant problems.
First, compliance frameworks often become checkbox exercises rather than drivers of genuine security improvement. Organizations focus on meeting specific regulatory requirements rather than addressing their actual threat landscape. A company might implement the precise security controls mandated by regulation while remaining vulnerable to attack vectors that fall outside the regulatory scope.
Second, sector-specific frameworks create inconsistency and inefficiency. A company operating in multiple sectors or multiple jurisdictions must navigate different, sometimes contradictory, requirements. Resources get devoted to compliance management rather than security improvement. The burden falls particularly heavily on smaller organizations that lack specialized compliance teams.
Third, regulatory approaches often lag significantly behind threat evolution. The regulatory process is inherently slow—developing regulations requires extensive stakeholder consultation, legal review, and political approval. By the time regulations are implemented, the threat landscape may have shifted substantially. This creates a perpetual game of catch-up where regulations address yesterday’s threats while organizations face tomorrow’s challenges.
Perhaps most problematically, the existence of compliance frameworks can create a false sense of security. Organizations and policymakers alike may assume that if companies are meeting regulatory requirements, critical infrastructure is adequately protected. This assumption is frequently invalid. Regulatory baselines typically represent minimum acceptable standards rather than best practices, and compliance with outdated standards provides little protection against sophisticated adversaries.
The International Dimension: Borders Mean Nothing to Bits
Cyber operations respect no national boundaries. An attack can be launched from one continent, route through infrastructure in a dozen countries, target victims in another region entirely, and be attributed to actors in yet another location. This fundamental reality of cyberspace creates profound challenges for national cybersecurity strategies that remain largely bound by traditional concepts of sovereignty and jurisdiction.
The UK’s cyber action plan, like most national strategies, focuses primarily on domestic resilience and capabilities. Yet British critical infrastructure faces threats from adversaries operating globally, often exploiting infrastructure and services located outside UK jurisdiction. A coordinated international response would seem essential, yet international cooperation on cybersecurity remains limited and inconsistent.
Several factors constrain international cooperation. Nations have different threat perceptions, different relationships with potential adversary states, different legal frameworks governing surveillance and response, and different economic interests that may conflict with security considerations. The result is that while threats are global, responses remain predominantly national.
This creates exploitable gaps. Adversaries can operate from jurisdictions that lack strong cybersecurity laws, refuse to cooperate with international investigations, or actively provide safe harbor for cyber operations. They can route attacks through infrastructure in countries with limited monitoring or attribution capabilities. They can exploit differences in regulatory approaches, targeting the least protected elements of global supply chains or infrastructure networks.
Some multilateral initiatives have emerged—the Budapest Convention on Cybercrime, various United Nations processes, regional frameworks in the European Union and elsewhere—but these remain limited in scope and effectiveness. Fundamental disagreements about acceptable state behavior in cyberspace, the role of international law, and mechanisms for accountability persist among major powers.
For critical infrastructure operators, this international dimension creates additional complexity. A company operating telecommunications networks must consider threats from multiple nation-states, criminal organizations operating from various jurisdictions, and insider threats from a globally distributed workforce. National strategies that focus narrowly on domestic resilience provide little guidance for navigating this complex international threat landscape.
The Economic Calculation: Who Pays for Security?
Underlying many policy gaps is a fundamental economic question: who should bear the cost of cybersecurity for critical infrastructure? This question often goes unasked in policy documents, yet it shapes implementation in profound ways.
Private companies operate according to economic logic. Security investments must be justified in terms of risk reduction, regulatory compliance, or competitive advantage. A power company evaluates cybersecurity spending against other capital expenditures and operational costs. If security investments reduce profits without generating offsetting benefits, market pressures push against making them.
This creates a systematic underinvestment problem in cybersecurity for critical infrastructure. The costs of security measures fall directly on the company making them, while the benefits—preventing disruptions that could affect millions of people or national security—accrue largely to society. This is a classic economic externality, where private costs and social benefits misalign.
Government-focused cyber strategies largely sidestep this economic reality. They call for enhanced resilience and improved defenses but often provide neither the regulatory requirements that would compel investment nor the public resources that would offset private costs. The result is a policy that amounts to exhortation rather than enablement.
Some policy approaches attempt to address this economic challenge. Regulatory requirements can force minimum security investments, though they face the limitations discussed earlier. Tax incentives or direct subsidies can help offset costs, though these remain rare in practice. Information sharing and technical assistance can provide value without direct financial transfer, though these too remain limited.
The fundamental question persists: if critical infrastructure protection is genuinely a national security priority, as virtually every national strategy claims, why do policies leave the financial burden primarily on private entities operating according to market logic? The disconnect between strategic rhetoric and resource allocation reveals the limits of current policy thinking.
What Effective Policy Would Actually Look Like
Understanding the gaps and limitations in current approaches points toward what more effective cybersecurity policy for critical infrastructure protection might encompass. While no simple solution exists, several elements would likely need to be present in any truly comprehensive strategy.
First, effective policy would need to establish clear baseline security requirements for critical infrastructure across sectors, with requirements calibrated to risk levels and organizational capabilities. These requirements should focus on outcomes and capabilities rather than specific technologies or implementations, allowing organizations flexibility in how they achieve security objectives while establishing clear accountability for results.
Second, policy should create robust mechanisms for government-to-private sector information sharing. This means not just periodic briefings or sanitized reports but timely, actionable intelligence about specific threats, vulnerabilities, and attack techniques. It also means creating legal frameworks that protect companies from liability for sharing information about incidents and vulnerabilities, addressing one of the key barriers to information flow.
Third, effective policy would provide resources commensurate with requirements. If national security demands that critical infrastructure achieve certain security levels, governments should provide technical assistance, financial support, or other resources to enable compliance, particularly for smaller organizations with limited resources. This might include shared security operations centers, subsidized security assessments, or direct financial assistance for implementing specific security measures.
Fourth, policy should address supply chain security comprehensively, establishing frameworks for evaluating vendor risk, requirements for supply chain transparency, and potentially maintaining approved vendor lists for the most sensitive infrastructure components. This requires balancing security considerations against economic efficiency and innovation, but current approaches lean too far toward accepting risks in the name of efficiency.
Fifth, international cooperation must move beyond aspirational statements to operational reality. This includes mutual legal assistance treaties that enable rapid response to cross-border cybercrime, information sharing agreements that enable coordinated defense, and diplomatic efforts to establish norms of acceptable state behavior in cyberspace that are actually enforced through consequences for violations.
Sixth, policy should create clear accountability structures. When critical infrastructure is compromised due to inadequate security, there should be mechanisms for determining whether the operator met reasonable security standards and consequences if they did not. Simultaneously, when government agencies possess threat intelligence relevant to critical infrastructure protection but fail to share it effectively, there should be accountability for those failures as well.
Seventh, effective policy would establish dedicated research and development programs focused on critical infrastructure protection. This includes developing security technologies suited to industrial control systems and operational technology environments, creating better tools for detecting and responding to sophisticated attacks, and building the workforce pipeline needed to staff cybersecurity roles across the economy.
Finally, policy should acknowledge and plan for the reality that despite all defensive measures, sophisticated adversaries will sometimes succeed. This means establishing robust incident response capabilities, recovery plans, and resilience measures that enable critical services to continue or quickly resume even after compromise. It also means creating clear communication protocols so that public officials, affected populations, and partner organizations receive accurate, timely information during crises.
The Path Forward: From Rhetoric to Reality
Implementing comprehensive critical infrastructure protection policies faces significant political, economic, and technical challenges. The current approach—government-focused strategies with limited private sector requirements—persists partly because it avoids difficult questions about cost allocation, regulatory burden, and government authority over private enterprise.
Yet the threat landscape makes these questions unavoidable. AI-enabled attacks, sophisticated state-sponsored campaigns, and growing supply chain vulnerabilities mean that the gap between government security and critical infrastructure protection represents an increasingly exploitable weakness. The question is not whether this gap will be addressed but whether it will be addressed proactively through thoughtful policy or reactively following a catastrophic incident.
Several encouraging developments suggest that policy evolution is possible. The European Union’s NIS2 Directive represents a more comprehensive approach to critical infrastructure protection than many national strategies, though implementation challenges remain. The United States has taken steps toward mandatory reporting of incidents affecting critical infrastructure and increased information sharing through sector-specific agencies. Australia’s critical infrastructure protection legislation establishes enhanced government powers during serious cyber incidents.
These initiatives have limitations and critics, but they represent movement toward recognizing that critical infrastructure protection cannot be treated as primarily a private sector responsibility. The question is whether other nations, including the UK, will follow similar paths or whether policy will continue to emphasize government resilience while treating private sector protection as secondary.
The challenges are real. Expanding regulation faces resistance from industry groups concerned about compliance costs and implementation burdens. Providing public resources for private sector security faces skepticism from those who question whether governments should subsidize corporate cybersecurity. Creating international frameworks faces the persistent obstacles of divergent national interests and fundamental disagreements about acceptable state behavior.
Yet these challenges must be weighed against the alternative. Every major cybersecurity incident affecting critical infrastructure in recent years has prompted the same cycle: initial shock, promises of improved security, incremental policy adjustments, then a gradual return to complacency until the next incident. Breaking this cycle requires acknowledging that current approaches are inadequate and committing to the difficult work of developing and implementing comprehensive alternatives.
Beyond the Fortress Walls
The medieval analogy introduced earlier bears revisiting. The kingdom that fortifies its castle while leaving the town vulnerable eventually discovers that the distinction between castle and town is largely artificial. When the grain stores burn, the castle starves. When the blacksmiths flee, the castle’s weapons cannot be repaired. When the population loses confidence in the kingdom’s ability to protect them, the castle’s walls become irrelevant.
Modern nations face a parallel reality. Government networks and critical infrastructure are not separate domains but interconnected elements of a functioning society and economy. Protecting one while neglecting the other is not a partial success; it is a fundamental strategic failure that adversaries will inevitably exploit.
The UK’s refreshed cyber action plan and similar strategies from other nations reveal governments beginning to grapple with evolving threats—AI-enabled attacks, supply chain vulnerabilities, persistent state-sponsored campaigns—but doing so through frameworks that remain fundamentally oriented toward government rather than whole-of-nation resilience. This represents incremental progress but falls far short of what the threat landscape demands.
What’s needed is a fundamental reframing of cybersecurity policy to recognize that in the digital age, there is no meaningful distinction between government security and critical infrastructure security. Both must be addressed comprehensively, with resources, requirements, and accountability distributed appropriately between public and private sectors based on capability and responsibility rather than ownership status.
This reframing requires difficult conversations about costs, authority, and responsibility. It requires moving beyond voluntary frameworks and aspirational strategies toward binding requirements and provided resources. It requires international cooperation that overcomes national differences and economic interests. It requires sustained political commitment and public resources even in the absence of dramatic incidents that force temporary attention to these issues.
The alternative is to continue fortifying the castle while the village remains vulnerable, hoping that adversaries will continue to respect a distinction between government and critical infrastructure that exists in policy documents but not in strategic reality. History suggests that hope is not a strategy, and adversaries reliably exploit whatever vulnerabilities defenders leave available.
The digital transformation of society has created dependencies and vulnerabilities that previous generations never faced. Meeting this challenge demands policy innovation commensurate with the technological change that created it. Current cybersecurity strategies, for all their improvements, remain rooted in frameworks developed for a different era facing different threats. The gap between what’s needed and what’s being done grows wider with each advance in offensive capabilities and each expansion of digital dependency.
Closing this gap will require acknowledging uncomfortable truths: that market forces alone will not generate adequate security for critical infrastructure, that government focus on protecting its own networks is necessary but insufficient, that international threats demand international responses even when cooperation is difficult, and that genuine security requires resources and authorities that current political constraints make challenging to provide.
These are not easy acknowledgments or simple problems. But they are the challenges that policymakers must address if national cybersecurity strategies are to be more than elegant documents that describe intentions while failing to prevent catastrophic outcomes. The fortress cannot thrive while the village burns, and in the digital age, we are all living in the village, whatever the strategic documents might say.

Leave a comment