Vladimir Tsakanyan
Setting the Stage: A New Kind of Warfare
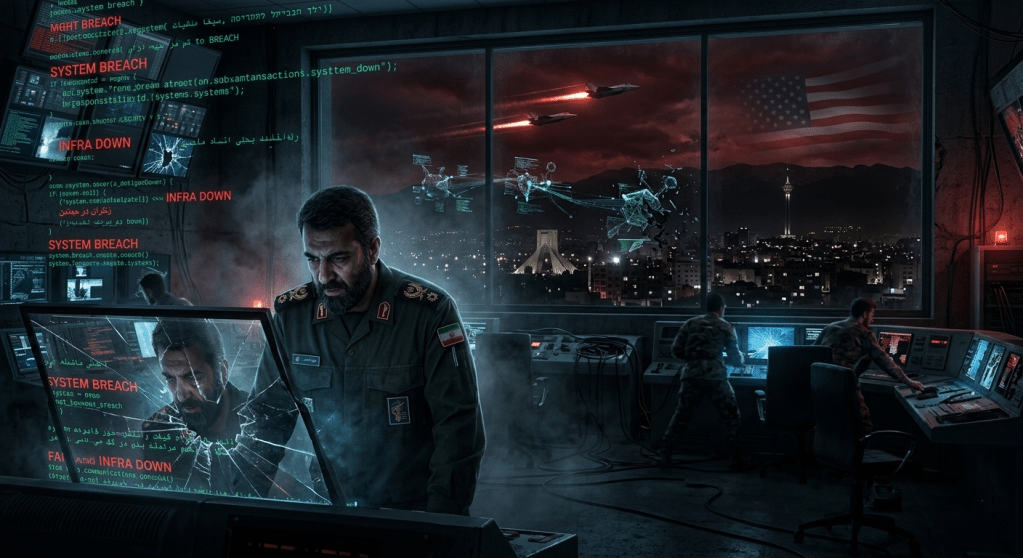
On February 28, 2026, the world witnessed something unprecedented. As Israeli fighter jets and cruise missiles struck IRGC command centers under Operation “Roar of the Lion,” a simultaneous digital offensive plunged Iran into near-total darkness. Internet connectivity in Iran collapsed to just 4% of normal traffic, a near-complete national shutdown, while critical infrastructure, official news sites, and security communications systems stopped functioning, leaving the Iranian leadership in a communications blackout both domestically and internationally.
This was not an isolated event. It was the culmination of years of escalating cyber conflict — and its consequences will reshape the geopolitical order for years to come, most critically for the United States.
The Historical Arc: From Stuxnet to Total Blackout
To understand the weight of what happened, context is essential. Israel has always been among the most capable cyber-offensive nations in the world, with a lineage tracing back to Stuxnet in 2010, the virus that destroyed Iran’s uranium centrifuges. What we are witnessing today is not improvisation — it is the maturation of a doctrine decades in the making.
The June 2025 Israel-Iran war was the dress rehearsal. In the brief but intense conflict from June 13 to June 25, 2025, battles raged not only in the skies but across cyberspace. The pro-Israel hacker group known as Predatory Sparrow crippled Iran’s Bank Sepah and burned around $90 million in cryptocurrency from the Iranian exchange Nobitex, delivering a strategic blow akin to a precision strike — one designed to disrupt funding flows and sow domestic chaos.
By 2026, Israel had upgraded from surgical financial disruption to total information blackout — a qualitative leap that signals a new chapter in 21st-century warfare.
What Was Actually Targeted and Why It Matters
The cyberattack was not random. Its architecture was deliberate and strategically layered:
Command and Control Disruption: By severing security communications during kinetic strikes, Israel neutralized Iran’s ability to coordinate a real-time military response. A blinded general cannot command troops.
Propaganda Infrastructure: Attackers hacked and hijacked Iranian state media to broadcast anti-regime messages, coinciding with physical strikes on the IRIB headquarters. Israel has established a pattern of treating enemy-affiliated media as military targets rather than journalistic institutions — operations that require advanced capabilities to penetrate.
Financial System Sabotage: Iran’s Bank Sepah, which has ties to the IRGC, was hacked resulting in widespread service outages. Nobitex, Iran’s largest cryptocurrency exchange with links to the IRGC and associates of Supreme Leader Khamenei, was attacked and approximately ninety million dollars in crypto assets were subsequently “burned,” rendering them permanently inaccessible.
Psychological Warfare: Iran’s cyber units responded by flooding Israelis with spoofed emergency alerts warning of fabricated fuel shortages and fake terrorist threats, mimicking official communications systems. In cyberspace, perception is a crucial part of the battle.
Immediate Consequences and Strategic Outcomes
For Iran
The regime suffered a multi-domain humiliation. Its military could not coordinate effectively. Its banking system failed its citizens at a moment of national crisis. Its propaganda apparatus — the tool Tehran relies on to maintain legitimacy — was turned against it, broadcasting anti-Khamenei messages to the Iranian people. The psychological damage of that last point cannot be overstated: regimes derive power from the appearance of invulnerability.
Iran now faces a painful strategic dilemma. Experts suggested Iran may be reserving more disruptive cyber capabilities in case of further escalation — meaning Tehran is rational enough to understand that deploying its full cyber arsenal now could invite even more devastating retaliation. It is deterrence through demonstrated capability.
For the Norms of Warfare
This conflict has definitively answered a question strategists have debated for a decade: are cyberattacks a legitimate companion to kinetic warfare? The answer is now unambiguously yes. The Iran-Israel war of 2025 stands as a testament and a warning: cyberpower is now a firmly entrenched extension of conventional force, inseparable from the calculus of modern warfare.
For the Global Threat Landscape
AI lowers barriers to entry for sophisticated cyberattacks, making them accessible to smaller states and non-state actors. Smaller actors, including terrorist organizations and hacktivist groups, can now employ automated hacking tools that streamline attack methods previously limited to well-resourced state actors. Israel’s success will be studied and emulated — not just by allies, but by adversaries of the United States.
The American Dimension: Why This Should Keep Washington Up at Night
The question Americans need to urgently ask is not “what happened to Iran?” — it’s “what comes next for us?”
1. Iran Will Retaliate Against American Targets
Iran does not separate Israel from the United States in its threat doctrine. American support for Israeli operations — diplomatically, militarily, and in intelligence-sharing — makes U.S. infrastructure a legitimate target in Iranian strategic thinking. APT35, linked to Iran’s Revolutionary Guard Corps, primarily targets American, European, and Middle Eastern government, defense, and critical infrastructure organizations, and has a track record of long-term, resource-intensive campaigns using spearphishing, social engineering, and custom malware. These campaigns will intensify.
History provides a template: In 2014, an Iranian-backed group caused $40 million in damages to a Las Vegas casino after its CEO expressed support for stronger action against Iran. Now imagine that calculus applied after a conflict of this magnitude.
2. The Proxy Network Will Activate
Iran does not need to attack America directly. It has a global network of cyber proxies. Among the top hacktivist groups targeting Israel in 2025 were the pro-Iran Arabian Ghosts, Black Ember, pro-Palestinian Mr. Hamza, and pro-Russian NoName057(16) — the latter illustrating the dangerous convergence of Iranian and Russian cyber interests, both of which are fundamentally hostile to American power.
3. American Critical Infrastructure Remains Dangerously Exposed
While state-level cybersecurity may achieve greater balance between offense and defense, civilian-targeted asymmetric cyber warfare is set to disproportionately tip the scale in favor of offensive actors. Civilian infrastructure lacks the resources and advanced AI-driven cybersecurity systems necessary for robust defense. America’s power grids, water systems, financial networks, and hospital systems present exactly these soft targets.
4. The Precedent Problem
Every tactic Israel used against Iran — communications blackout, financial system sabotage, media hijacking — now exists as a documented playbook. America’s adversaries, from Iran to China to Russia’s GRU, will have analyzed every byte of these operations. The United States cannot assume it is immune to the same playbook being deployed against New York, Houston, or Washington D.C.
5. Escalation Dynamics and the U.S. Role
Iran’s IRGC fired missiles targeting U.S. military bases in Qatar and Iraq in response to American strikes on Iranian nuclear facilities in June 2025. With the United States now directly embedded in this conflict, American military and diplomatic assets worldwide face elevated cyber and kinetic risk. U.S. lawmakers were already planning Iran war powers votes as Trump weighed further strikes, indicating Washington’s entanglement is deepening, not receding.
The Longer Strategic Horizon
Three developments will define how this plays out for America:
The AI Arms Race in Cyberspace. AI-driven anomaly detection tools are more effective at identifying compromises than traditional rule-based systems, but for well-resourced actors on both sides, the introduction of AI may lead to stalemate dynamics rather than decisive advantages — a constant probing of novel vulnerabilities. The United States must invest massively in AI-driven cyber defense or risk falling behind.
The Normalization of Infrastructure Warfare. Once a state has demonstrated that banking systems, communications networks, and energy infrastructure are legitimate wartime targets — and suffered no international legal consequences — the permission structure for other actors expands. China’s calculus about Taiwan, Russia’s calculus about NATO — both are watching.
Iran’s Long Game. A humiliated Iran with a battered military but an intact cyber program is arguably more dangerous than a powerful Iran. Asymmetric actors with nothing left to lose are unpredictable. It is easy to imagine a darker scenario: what if Iran had knocked out parts of Israel’s power grid, or caused a financial meltdown? That scenario could yet materialize — against American targets.
Conclusion: America Must Act Now
Israel’s historic cyberattacks against the Islamic Republic represent more than a bilateral conflict milestone. They are a seismic event in the architecture of modern warfare, one that compresses the timeline for every scenario American defense planners have been modeling for years.
The United States faces three immediate imperatives: harden civilian critical infrastructure with the urgency of a wartime posture; recalibrate intelligence-sharing frameworks with allies to include real-time cyber threat feeds; and develop clear public deterrence doctrine communicating the consequences of Iranian cyber aggression on American soil.
The digital fog that blanketed Tehran on February 28, 2026 will not stay confined to the Middle East. In the interconnected world of 21st-century conflict, what begins as Israel’s war has a way of becoming America’s problem — and the clock is already running.
Analysis based on open-source intelligence, Atlantic Council reporting, NSFOCUS threat intelligence, Radware global cyber threat data, and Times of Israel national security coverage.

Leave a comment