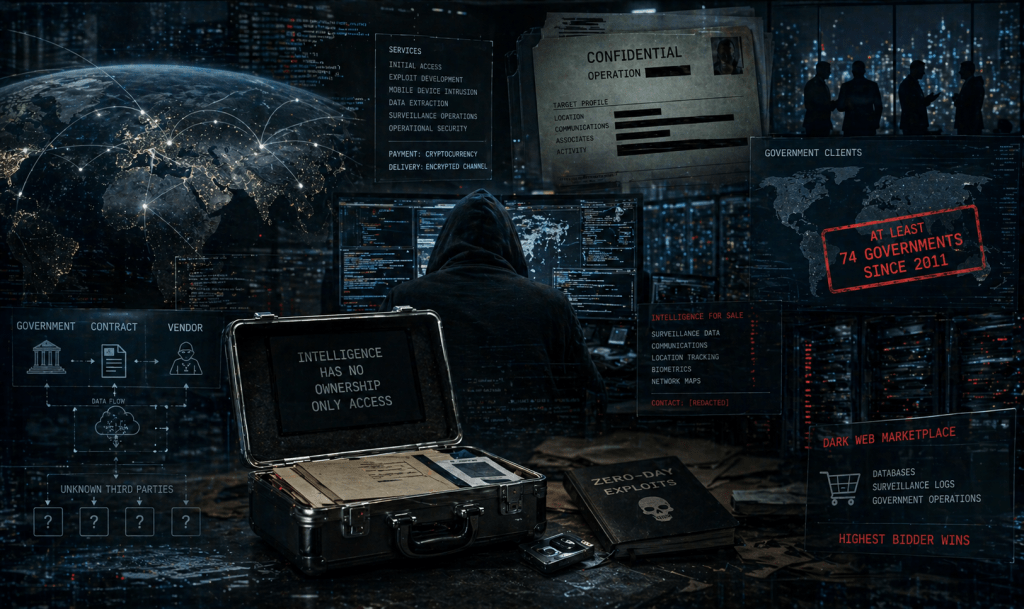
At least 74 governments have hired private hackers since 2011. The intelligence they collected didn’t always stay in their hands.
By Vladimir Tsakanyan, PhD · Center for Cyber Diplomacy and International Security · cybercenter.space
A government commissions a private hacking firm to penetrate the communications of a foreign dissident. The operation succeeds. Encrypted messages are extracted. Movements are mapped. A network of associates is identified. The contracting government receives its product.
What it does not receive — what no contract specifies, what no export licence governs, and what no international framework currently addresses — is any assurance about what happens to that intelligence after it leaves the vendor’s infrastructure. Who else has seen it. Whether it has been retained. Whether it has been sold.
This is the question at the centre of the cyber mercenary economy that almost no government is willing to ask out loud.
The Market and Its Scale
The commercial trade in offensive cyber capability is no longer a niche industry. Valued at $12 billion as of 2019 and growing rapidly, it now encompasses a global ecosystem of private firms offering services that were, a generation ago, the exclusive province of the world’s most sophisticated intelligence services: spyware capable of silently extracting the entire contents of a target’s device; zero-day exploits — previously unknown software vulnerabilities — purchased and stockpiled for use against specific targets; influence operation toolkits; destructive malware; and managed surveillance infrastructure operated as a service.
Since 2011, at least 74 national governments have leveraged cyber mercenaries for the use of spyware alone. The buyers range from democratic governments conducting legitimate counterterrorism operations to authoritarian regimes targeting journalists, opposition figures, and civil society activists. Cyber mercenary services appeal to governments in part because involving a third party helps conceal responsibility and avoid consequences for illegal or destructive behaviour.
The deniability is the product. It is what governments are paying for.
The Loyalty Problem
The mercenary relationship has always carried an inherent tension: the hired actor operates under a contract, not a flag. In cyberspace, that tension is structurally more dangerous than in any conventional context, because the product being traded is intelligence — and intelligence, once collected, does not observe the boundaries of its original transaction.
Private offensive cyber firms do not merely hand a tool to a government client and step away. In many operational architectures, the vendor retains access to the infrastructure through which the surveillance is conducted. Control over platforms and data becomes a source of leverage, not liability. The intelligence harvested through a commercial surveillance operation — the messages, the contacts, the location data, the network of relationships — resides, at least temporarily, in systems the contracting government does not own and cannot fully audit.
The downstream risk is not theoretical. In late 2025, stolen data from a cybersecurity firm with documented government ties was reportedly sold on the dark web — intelligence tradecraft, offensive tooling, and the records of state-sponsored operations, offered to the highest bidder by an actor with no relationship to any of the governments whose operations were exposed. The secrets moved. They always move.
When a vendor firm is itself breached — as has occurred in documented cases — the collected intelligence of every client operation it has conducted becomes potentially accessible to the attacker. When a firm is acquired, its operational logs transfer with the corporate entity. AI-driven hacking has further fueled the growth of cyber mercenaries, making sophisticated attacks easier to execute and harder to regulate. And when individual operatives move between firms — as they routinely do in this sector, where the talent pool is small and the commercial incentive to change employers is high — they carry institutional knowledge of operations that no security clearance framework was ever designed to govern.
Analyst note
The intelligence custody problem is the feature of the cyber mercenary market that receives the least diplomatic attention and poses the greatest long-term strategic risk. A government that believes it has conducted a contained covert operation through a commercial platform has, in most cases, conducted a shared one. The chain of custody for secrets harvested through private infrastructure does not end where the contracting government assumes it does. It ends where the market decides.
The Governance Gap
Absent meaningful international guardrails, the cyber mercenary industry has enabled human rights abuses, lowered the barrier to entry for advanced cyber weapons, and further complicated the challenge of cyber accountability. Existing export control frameworks were built for a different era and have proven consistently inadequate. Blacklisting individual firms produces rebranding, not restraint. Bilateral sanctions imposed by a single government leave the broader market untouched. Some mercenary groups have argued that the legal principle of sovereign immunity should extend to private actors selling to government clients — a position that, if accepted, would effectively immunise the entire industry from legal accountability.
No binding multilateral instrument governing the commercial trade in offensive cyber capability is currently under serious negotiation. The political declarations produced by allied governments since 2023 remain statements of intent. They impose no obligations, create no verification mechanisms, and establish no consequences for non-compliance.
Bottom Line Assessment
The cyber mercenary economy is, at its core, a market for secrets — and like every market, it optimises for the interests of its participants, not its clients. Governments that outsource offensive cyber capability to private actors are not conducting contained intelligence operations. They are entering a commercial ecosystem in which the intelligence they collect is also an asset to the vendor who collected it, to the vendor’s other clients, to the intelligence services monitoring the vendor’s home jurisdiction, and to any actor capable of breaching the vendor’s infrastructure.
Conflict is becoming commercially captured. Battlefield telemetry is morphing into a tradable asset. The secrets being sold in this market are not sold only once. They circulate. They accumulate. They find their way to actors no contracting government authorised and no diplomatic framework anticipated.
The hired gun remembers everything it was asked to do. And it is not bound, by any enforceable rule, to keep that memory to itself.
Cyber Mercenaries · Hack-for-Hire · Digital Sovereignty · Cyber Espionage · Intelligence · Commercial Spyware · Cyber Diplomacy · Vladimir Tsakanyan

Leave a comment