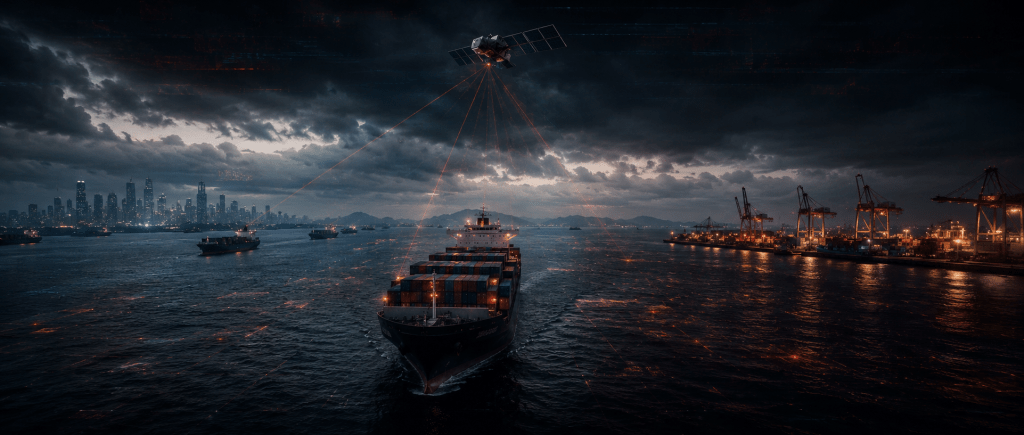
Maritime cyber incidents doubled in 2025. Ninety percent of global trade moves by sea. And the vessels carrying it run on software architecture that was never designed to be connected, governed by regulations that were never designed to be enforced, crossing chokepoints that were never designed to survive a coordinated digital attack.
By Vladimir Tsakanyan, PhD · Center for Cyber Diplomacy and International Security · cybercenter.space
In the first half of 2024, security researchers catalogued 23,400 malware detections and 178 ransomware attacks across just 1,800 monitored vessels. Ships were bricked — rendered entirely inoperable by encrypted systems — and forced to anchor in open water for days while crews waited for IT recovery teams to reach them. By the time the full 2025 figures were published, the number of maritime cyber incidents had surged 103 percent compared to the previous year. The growth rate had more than doubled in twelve months.
The global maritime industry carries approximately ninety percent of international commerce. It operates through a handful of chokepoints — the Strait of Hormuz, the Suez Canal, the South China Sea, the Strait of Malacca — whose disruption, even for days, cascades through supply chains, energy markets, and food systems on multiple continents simultaneously. The 2021 blockage of the Suez Canal by a single grounded container vessel, an entirely non-cyber event lasting six days, cost an estimated nine billion dollars per day in delayed trade.
That was one ship. Stuck. By accident.
The attack surface that now exists across the maritime domain is not one ship. It is a globally distributed network of thousands of vessels, hundreds of port systems, dozens of critical chokepoints, and an operational technology infrastructure that was designed before the internet existed, connected to it anyway, and secured as an afterthought — if it was secured at all.
The Architecture of Vulnerability
A modern commercial vessel is, in terms of its digital infrastructure, two machines occupying the same hull. Approximately fifty percent of its systems are information technology — office networks, crew communications, cargo documentation, data-sharing with port authorities. The other fifty percent are operational technology: the systems that control propulsion, steering, navigation, engine management, ballast tanks, and cargo handling. These are the systems that, if compromised, do not produce a data breach. They produce a navigation failure in a congested strait, a propulsion loss in contested waters, or a cargo system malfunction at a port handling ten thousand containers a day.
The convergence of these two layers — designed to be separate, connected by the operational pressures of digital transformation — is the primary vulnerability that sophisticated attackers have learned to exploit. Nautical charts, updated every two weeks, are typically downloaded to officer laptops and transferred to navigation computers via USB drives. Without malware scanning — a capability that many vessels still do not deploy — these drives cross the boundary between the internet-connected IT layer and the operationally critical OT layer, carrying whatever they have acquired along the way. Ransomware documented in the Maritime Cyber Attack Database has followed precisely this path: entering through a port Wi-Fi connection or a Starlink terminal, traversing the IT-OT boundary through an unscanned USB transfer, and reaching systems controlling navigation or cargo operations that their operators assumed were isolated from external networks.
They were not isolated. They had simply never been tested.
Analyst note
The IT-OT convergence problem in maritime is structurally identical to the problem that has made industrial control systems and critical infrastructure vulnerable on land — with one additional dimension that land-based infrastructure does not share. A vessel in transit is a sovereign jurisdiction at sea, governed by the flag state whose registry it carries, subject to the port state’s regulations when it calls at port, and effectively ungoverned in the open ocean in between. A cyberattack that begins when the vessel connects to port Wi-Fi in one jurisdiction, propagates through the ship’s systems while it transits international waters, and activates when the vessel enters a contested strait falls under the legal authority of three different regulatory regimes simultaneously, none of which has the operational capacity to respond to a cyber incident unfolding on a ship in motion on the open sea.
GPS Spoofing and the War on Navigation
The most operationally immediate cyber threat in the maritime domain is not ransomware. It is the systematic manipulation of the positioning and navigation data on which vessels depend for safe transit through the world’s most congested and geopolitically contested waterways.
GPS spoofing — the broadcast of false positioning signals that override genuine satellite data — has become a standard tool of state-level hybrid warfare applied to the maritime environment. In the Red Sea, the Baltic Sea, the South China Sea, the Caribbean, and the wider Middle East, documented spoofing incidents have caused vessels to appear, on their own navigation systems and on publicly visible tracking platforms, thousands of kilometres from their true position. In some cases, vessels have reported their navigation systems placing them over land. In others, the spoofing has been precise enough to create the appearance of a collision course that does not exist, triggering emergency manoeuvres with their own physical risks in busy shipping lanes.
The strategic logic behind maritime GPS spoofing is not difficult to reconstruct. A state actor with an interest in disrupting shipping through a specific chokepoint — whether to enforce a blockade, to create confusion cover for a physical operation, or simply to demonstrate the capacity to degrade navigation in contested waters — can achieve significant disruption through spoofing without firing a single kinetic weapon and while maintaining full deniability. The signal comes from somewhere. It can be attributed to no one. The vessel’s crew experiences a navigation anomaly. The incident report attributes it to equipment malfunction. The state actor notes the outcome and adjusts for next time.
The Red Sea and Strait of Hormuz have seen the most concentrated documented spoofing activity, closely correlated with the periods of highest geopolitical tension in those waterways. In the Baltic, spoofing incidents have been concentrated near Russian naval activity and have affected commercial vessels, civilian aircraft, and emergency services operating in Finnish, Estonian, and Lithuanian territorial waters. In the South China Sea, incidents have been documented in areas where competing sovereignty claims create overlapping zones of contested authority — precisely where navigation confusion serves the interests of the actor most invested in controlling the narrative of who was where and when.
The Shadow Fleet and Its Blind Spots
The geopolitical restructuring of global shipping — driven by sanctions, trade rerouting, and the deliberate fragmentation of established maritime commerce patterns — has produced a second-order cyber security problem that no regulatory framework has begun to address: the shadow fleet.
Sanctions evasion has driven a substantial portion of global oil and commodities trade into a fleet of vessels that operate outside the established frameworks of insurance, registration, flag state oversight, and port state control that nominally govern maritime security. These vessels turn off their AIS transponders — the system that broadcasts a ship’s identity, position, and course to other vessels and to maritime authorities — and transit through contested waters with no visible identity and no regulatory accountability. Their cyber security posture, to the extent that anyone has assessed it, is essentially unknown.
The shadow fleet is not merely a sanctions evasion problem. It is a cyber security blind spot of strategic significance. Vessels operating outside established regulatory frameworks have no incentive to comply with cyber security requirements, no access to the industry-wide threat intelligence sharing mechanisms that legitimate operators use, and no relationship with the port state authorities that would detect a cyber incident during a port call. They are, in the precise technical sense, ungoverned digital assets — vessels with operational technology systems, satellite communications, and navigation infrastructure that are connected to the same maritime digital ecosystem as legitimate shipping, but invisible to any of the governance mechanisms that nominally secure it.
In conflict-prone waters, the shadow fleet’s combination of AIS-off operation and unknown cyber posture creates conditions in which a compromised vessel — one whose navigation or communications systems have been manipulated by an external actor — could be positioned and directed in ways that its owners, its crew, and the maritime authorities in whose waters it operates cannot detect or attribute.
Analyst note
The shadow fleet represents the maritime domain’s version of the ungoverned identity space documented in stateless populations and failed state digital infrastructure: a set of operational assets that exist within the shared maritime ecosystem, dependent on its digital infrastructure, but outside the governance frameworks that nominally manage its security. The cyber threat does not respect the boundary between the legitimate fleet and the shadow fleet. Malware propagates through port connections that both fleets share. GPS spoofing affects navigation systems regardless of whether the vessel’s AIS transponder is transmitting. The shadow fleet’s ungoverned status does not insulate it from cyber threats. It insulates the threat actors who use it from accountability.
The Chokepoint Scenario
The convergence of GPS spoofing, IT-OT vulnerability, and geopolitical tension produces a scenario that maritime security researchers have described in classified and open-source assessments with increasing specificity: a coordinated cyber operation targeting shipping at a critical chokepoint, designed to create physical disruption that achieves strategic objectives without triggering the threshold for armed conflict.
The Strait of Hormuz carries approximately twenty percent of the world’s oil supply. The Strait of Malacca carries approximately forty percent of global trade. The Suez Canal, when fully operational, handles twelve percent of global trade volume — a proportion that has demonstrated, through two years of Red Sea crisis rerouting, its capacity to reshape global supply chains, energy prices, and shipping economics when disrupted.
A coordinated cyber operation at any of these chokepoints does not need to sink ships to achieve its objectives. It needs only to create sufficient navigation uncertainty — through spoofing that produces conflicting position data across multiple vessels simultaneously — to force the precautionary closure of the transit lane, the anchoring of vessels pending verification of their positioning systems, and the cascade of delays, diversions, and cost increases that follow a chokepoint disruption of even forty-eight hours. The physical result is indistinguishable, to global markets and supply chains, from a kinetic disruption. The perpetrator is invisible. No red line has been crossed. No Article 5 has been triggered. No retaliatory strike can be justified on the basis of a GPS signal from an unlocated transmitter.
In 2026, AI agents are expected to perform up to ninety percent of the attack lifecycle — from vulnerability analysis to data exfiltration — without human intervention in the loop. Applied to maritime targeting, this means the reconnaissance, timing, and execution of a spoofing operation across multiple vessels in a congested chokepoint can be automated to a degree that compresses the window between the decision to act and the operational effect to a timeframe that human response cannot match.
The Regulatory Illusion
The International Maritime Organisation has issued guidelines on cyber risk management. Flag states have begun incorporating cyber requirements into their registry conditions. Industry bodies have published standards and frameworks. Since July 2024, major registries have mandated cyber-protected systems with secure-by-design principles. In 2026, new international standards — IACS UR E26 and E27 — are becoming fully enforceable, with the prospect of vessels failing certification losing sailing credentials or being denied port entry.
This is meaningful progress. It is also, in its current form, inadequate to the threat environment that the 2025 incident data describes.
The regulatory framework is flag-state based, which means its enforcement depends on the maritime registry whose flag a vessel flies. Registries vary enormously in their capacity and their inclination to enforce cyber security requirements. A vessel flagged to a registry that lacks the technical capacity to assess cyber compliance is, for practical purposes, ungoverned — regardless of what the international standards nominally require. The shadow fleet, by definition, operates outside all of this. And the speed at which the threat environment is evolving — AI-driven attacks, autonomous exploit chains, GPS manipulation as a standard hybrid warfare tool — exceeds, by a substantial margin, the speed at which regulatory frameworks can be drafted, negotiated, ratified, and enforced across the jurisdictional complexity of the maritime domain.
The knowledge gap compounds the regulatory gap. Mariners are trained extensively in navigation, engineering, and safety. Cyber expertise at sea remains limited. In the engine room and on the bridge, the personnel most likely to be the first to notice a cyber anomaly are also the least likely to recognise it as one, or to know what to do about it, or to have the communications architecture to report it to anyone capable of responding in time.
Bottom Line Assessment
The maritime domain is the world’s most critical infrastructure and its most comprehensively neglected cyber security frontier. Ninety percent of global trade, twenty percent of global oil supply, and the connectivity of a globalised economy depend on shipping that now runs on deeply integrated digital systems, crosses chokepoints where GPS manipulation is a documented and regular occurrence, and is governed by a regulatory framework that is jurisdictionally fragmented, technically outpaced, and structurally blind to the shadow fleet that a geopolitically fractured world has generated at scale.
The 103 percent surge in maritime cyber incidents in 2025 is not a statistical anomaly to be smoothed over in the next reporting cycle. It is a signal — that the attack surface has been identified, that the capabilities to exploit it are maturing, and that the actors most interested in the strategic disruption of global trade have noted both the vulnerability and the absence of any credible deterrent response.
The sea has always been a domain of conflict. What is new is that the weapons being brought to it are invisible, the perpetrators are deniable, the targets are the digital systems that every vessel carries and nobody has secured, and the consequences of a successful operation at a critical chokepoint could cascade through the global economy faster than any maritime authority in history has moved to respond.
The era of disconnected seas is over. The era of defended ones has not yet begun.
Maritime Cybersecurity · GPS Spoofing · Critical Infrastructure · Chokepoints · Shadow Fleet · OT Security · Hybrid Warfare · Supply Chain · Vladimir Tsakanyan

Leave a comment